Android 2.3.6 And Ice Cream Sandwich More Vulnerable: Kaspersky
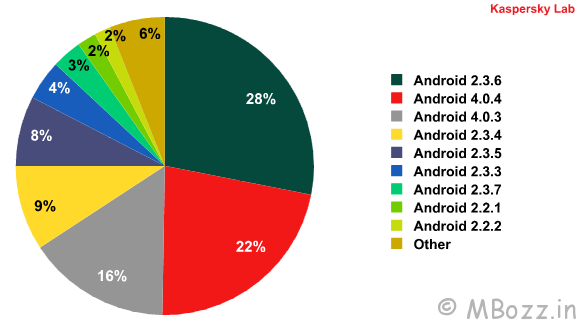
Analysis of mobile malware for Android OS by Kaspersky Lab experts in Q3 2012 revealed that the most popular targets among cyber criminals were Android versions 2.3.6 or Gingerbread, and Android 4.0 aka Ice Cream Sandwich. The rapid growth in the number of new mobile malicious programs for Android continued in the third quarter, prompting the specialists at Kaspersky Lab to identify the platform versions most frequently targeted by cybercriminals. Android 2.3.6 Gingerbread accounted for 28 per cent of all blocked attempts to install malware, while the second most commonly attacked version was the new 4.0.4 Ice Cream Sandwich, which accounted for 22 per cent of attempts.
“Although Gingerbread was released back in September 2011, due to the segmentation of the Android device market it still remains one of the most popular versions, which, in turn, attracts increased interest from cybercriminals,” commented Yuri Namestnikov, senior malware analyst, Kaspersky Lab. “The popularity of the most recent version of the Android OS – Ice Cream Sandwich – among virus writers can be explained by the fact that the devices running the latest versions of the OS are more suitable for online activities. Unfortunately, users actively surfing the web often end up on malicious sites.”
More than one half of all malware detected on user smartphones turned out to be SMS Trojans, i.e. malicious programs that steal money from victims’ mobile accounts by sending SMS messages to premium rate numbers.
The OpFake family has become the most widespread (38.3 per cent of all the malicious programs detected for Android) among all the mobile malware families. All the programs in this family disguise themselves as OperaMini. A fifth of the malicious programs detected on user devices are versatile Trojans, most of which belong to the Plangton family. After being installed on a device, these Trojans collect service data on the telephone, send it to the command server and wait for the cybercriminals’ commands. Specifically, malicious programs in this family can stealthily change bookmarks and the home page. Third place in the ranking was taken by the FakeInst family, whose members pretend to be installers for popular programs (17 per cent). These two types of malware are mostly distributed via so-called alternative app stores created by cybercriminals.
